Rethinking Vulnerability Disclosure Programs (VDPs)
Stop Gaslighting Business Owners
The cybersecurity world has a problem, and it’s one we don’t talk about enough. Business owners—already juggling a thousand responsibilities—are being gaslit into believing they must accommodate unethical behavior under the guise of "responsible disclosure." Let’s call this what it is: victim-blaming disguised as cybersecurity best practices.
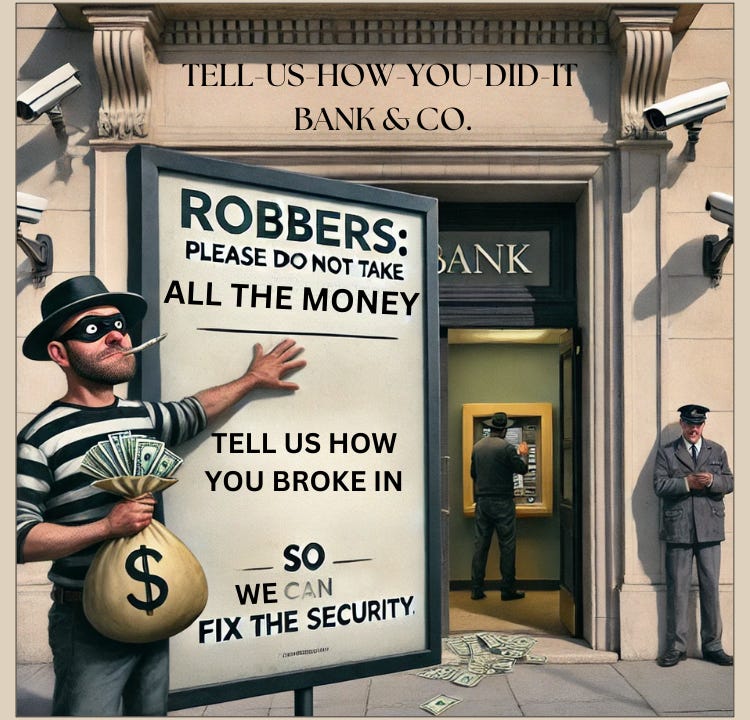
Imagine this scenario: a burglar breaks into your home and steals your belongings. But instead of being treated as the criminal they are, they leave you a note: "Your locks are terrible. Pay me for discovering this or hire me to fix them." Now, imagine the law starts to expect you to hang a sign on your front door inviting burglars to report what they find rather than ransack your house. Sounds ridiculous, right?
But this is exactly the narrative being pushed on business owners through Vulnerability Disclosure Programs (VDPs). This has to stop—not by rejecting collaboration or innovation, but by reframing the discussion toward thoughtful, proactive solutions that empower businesses to protect themselves.
What’s a VDP, and Why Does It Matter?
A Vulnerability Disclosure Program is marketed as a way for businesses to receive reports about security vulnerabilities in their systems. On the surface, it sounds like a good idea: if someone accidentally stumbles across a flaw, a VDP gives them a safe way to report it. That’s fair.
But here’s where things get murky: VDPs are being framed as necessary tools to manage “security researchers” who actively search for vulnerabilities in your systems without prior permission. This framing implies:
Unauthorized access is inevitable, so you’d better create a process to deal with it.
You, the business owner, bear responsibility for ensuring that unauthorized actors don’t face legal consequences for their actions.
Unauthorized probing of your network isn’t a crime—it’s a “social responsibility.”
Let me be clear: this is gaslighting, plain and simple.
Accidental Discovery vs. Criminal Behavior
There’s a massive difference between someone accidentally discovering a vulnerability and someone deliberately probing a system without permission.
Accidental Discovery: This happens when someone is using your website or application as intended and stumbles upon something they shouldn’t. Maybe a confidential file shows up in a search result, or an error reveals private information. These situations are unintentional and can happen to anyone—users, customers, or even employees. VDPs make sense here, offering a clear channel for reporting these findings.
Active Probing/Scanning: This involves someone intentionally testing your systems, looking for vulnerabilities without consent. This isn’t curiosity or “helpfulness”—it’s unauthorized access. No amount of good intentions can make it legal, ethical, or acceptable.
The problem? The current narrative around VDPs blurs this line. It paints those engaging in unauthorized access as “ethical researchers” instead of what they are: criminals.
A Neighborhood Watch for Cyberspace
The solution isn’t to turn businesses into fortresses or to shut down collaboration. Instead, we need to think of cybersecurity like a neighborhood watch. In a physical neighborhood, residents collaborate to protect their community, sharing insights and supporting one another to prevent crime. The same can be true in cyberspace: businesses, researchers, and policymakers can work together, but only with clear boundaries and shared respect.
Here’s how this can work:
VDPs for Accidental Discoveries: VDPs should focus on providing a path for people to report issues they come across unintentionally while using systems in good faith.
Pre-Authorization for Testing: Any active testing of systems by security researchers (e.g., ethical hackers, penetration testers) must be done with explicit permission and under explicit agreements, such as bug bounty programs, to ensure trust and accountability.
Empowering Businesses: Businesses should feel confident in their security without being forced into programs that feel more like damage control than prevention.
A neighborhood watch thrives when everyone understands their role and respects the boundaries of others. Cybersecurity can function the same way.
Why The Current VDP Narrative is Dangerous
When VDPs are framed poorly, they create serious problems:
It Normalizes Unauthorized Access: Treating unauthorized active probing as inevitable or even helpful sends the wrong message. It creates a culture where breaking into networks is seen as “ethical” instead of criminal.
It Victim-Blames Business Owners: Businesses are already doing their best to secure their systems. Suggesting they’re responsible for managing unauthorized actors only shifts blame away from the real problem: criminal behavior.
It Undermines Trust: Poorly framed VDPs risk eroding the trust between businesses, security researchers, and the public. We need collaborative solutions that empower businesses, not make them feel vulnerable.
What Needs to Change
VDPs need to be reframed to reflect their true purpose:
Focus on Accidental Discoveries: VDPs should serve people who unintentionally find vulnerabilities during normal, lawful activities—not those actively looking for flaws without permission.
Require Explicit Authorization for Researchers: Security researchers must operate under clear agreements with documented permission, like bug bounty programs, where their activities are pre-approved and transparent.
Empower Businesses to Take Control: Businesses should make security decisions based on thoughtful risk assessments—not because they’re told unauthorized access is inevitable.
This approach fosters collaboration without legitimizing unethical behavior.
A Call to Action
It’s time to rethink how we approach cybersecurity. Businesses don’t need to accommodate criminals or feel forced into programs that don’t align with their needs. Instead, they should be empowered to take control of their security with thoughtful, collaborative solutions.
To the Department of Justice, Cybersecurity and Infrastructure Security Agency, and policymakers: we need clear, practical guidelines that protect businesses and foster trust. Make it clear: VDPs should empower businesses to collaborate, not force them to accommodate unauthorized activity.
To business owners: Take back control. Thoughtful risk assessments, clear reporting processes, and collaboration can help you build a resilient and secure business. We don’t have to accept cybercrime as inevitable. Together, we can create a safer digital neighborhood—one where businesses thrive, vulnerabilities are addressed responsibly, and trust is the foundation of security.